Guard against security vulnerabilities in your software supply chain with Container Registry vulnerability scanning | Google Cloud Blog
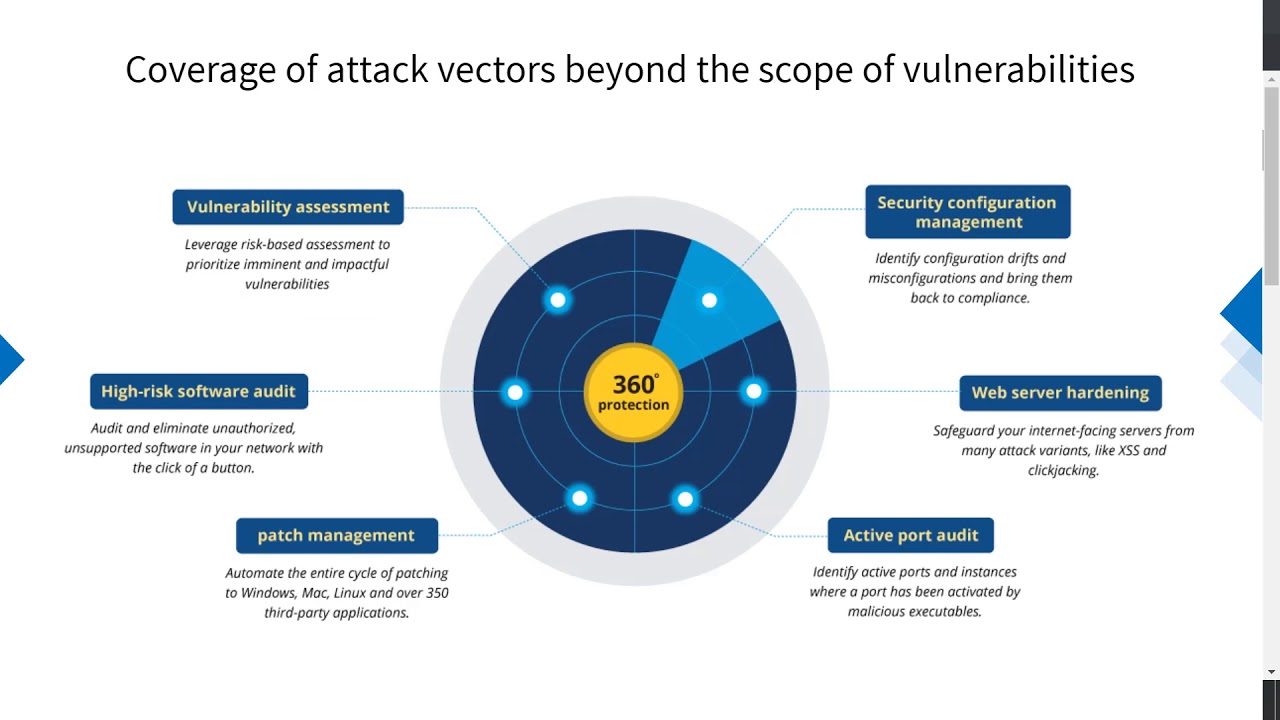
Linux Vulnerability Scanner | Linux Vulnerability Scanning Tool - ManageEngine Vulnerability Manager Plus

Use WPScan to scan WordPress for vulnerabilities on Kali - Linux Tutorials - Learn Linux Configuration
![Vulnerability scanning with nmap - Mastering Kali Linux for Advanced Penetration Testing - Second Edition [Book] Vulnerability scanning with nmap - Mastering Kali Linux for Advanced Penetration Testing - Second Edition [Book]](https://www.oreilly.com/library/view/mastering-kali-linux/9781787120235/assets/5c4d1dae-162c-44a0-8630-fcf21521f19a.png)